
Write something
Pinned
START HERE - For all the New Members
Welcome to the CyberCircle Community — your place to learn cybersecurity, grow your skills, and connect with others on the same journey. 🚀 Whether you’re a complete beginner, changing careers, or just getting started, you’re in the right place. What You’ll Find Here: 👉 Daily Quizzes: Fun and interactive Security+ prep to sharpen your skills. 👉 Important Cyber News: Stay updated with the latest industry news. 👉 Job Application Tips & Hacks: Insider tips to land your dream job in cybersecurity. 👉 Free Resources: Everything you need to kickstart your cybersecurity career for FREE. Create your First Post Introduce Yourself! 1. Your Name. 👋 2. Where You’re From. 🌍 3. Your Experience: e.g. Are you a beginner, making a career change, or a recent graduate? 🧑💻 4. What Inspired You to Start Cybersecurity? 💭 🛠 How to Use the Skool Platform 1. Have a Question? 🧐 Create a post in the Questions category. 2. Classroom Section: ✅ Access your free Cybersecurity Fundamentals Course 3. Calendar: 📅 Find upcoming calls or events. If you haven’t already share your linkedin Page and nectwork. I’ll also be here to support and answer your questions along the way. Let’s make this the BEST space for growing cybersecurity talent! ✨
0
0

Pinned
📌 Your Cybersecurity Roadmap 🔐🚀
If you're new or unsure where to start…Follow this step-by-step path and don’t overthink it. 🔰 PHASE 1: Understand the Basics (Week 1–2) Start here if you’re a beginner. Learn: - What cybersecurity is (Blue Team / Red Team / GRC) - Common threats (phishing, malware, brute force) - Basic networking (IP, DNS, ports) - Windows + Linux fundamentals 🎯 Goal: Understand how systems and attacks work 🧠 PHASE 2: Build Core Skills (Week 2–4) Now you start thinking like an analyst. Focus on: - Logs (Windows Event Logs, login activity) - SIEM basics (how tools like Splunk work) - Endpoint security (EDR tools like SentinelOne) - Identity & Access (logins, MFA, authentication) 🎯 Goal: Understand what to look for in real security data 🛠️ PHASE 3: Hands-On Practice (Week 3–6) This is where most people fail — don’t skip this. Do: - Set up a home lab (Windows + Linux) - Generate your own logs - Practice analyzing activity - Simulate simple attacks 🎯 Goal: Gain real experience (this is what gets you hired) 🔎 PHASE 4: Threat Detection (Week 5–8) Learn how to investigate like a real analyst. Focus on: - Login failures & suspicious activity - Event IDs (4625, 4769, etc.) - Malicious domains & phishing detection - OSINT tools (basic reputation checks) 🎯 Goal: Be able to analyze alerts confidently 📜 PHASE 5: Certifications (Parallel Track) Start preparing while learning. Recommended: - CompTIA Security+ (foundation) - CompTIA CySA+ (next level) 🎯 Goal: Validate your knowledge + boost your resume 💼 PHASE 6: Get Job Ready (Week 6–10) This is where you position yourself to get hired. Do: - Build a strong cybersecurity resume - Add your lab as “experience” - Optimize your LinkedIn - Start applying consistently 🎯 Goal: Start getting interviews 🎤 PHASE 7: Interview Prep (Ongoing) Prepare BEFORE you get the interview. Practice: - “Tell me about yourself” (cyber version) - Basic technical questions - Scenario-based answers
0
0

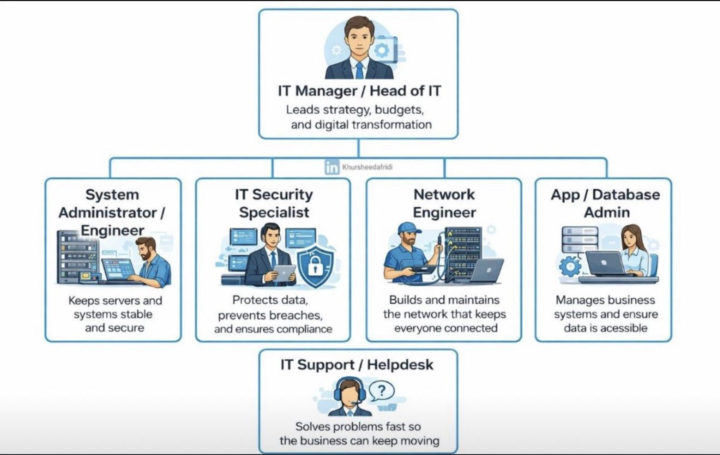
Understanding the IT Team Structure in Modern Organizations
A strong IT department is the backbone of any successful business. It’s not just about fixing computers—it’s about strategy, security, connectivity, and seamless operations. Each role in the IT team contributes to keeping the organization efficient, secure, and future-ready. 🔹IT Manager / Head of IT Drives overall IT strategy, manages budgets, and leads digital transformation. This role aligns technology with business goals and ensures all IT functions work together effectively. 🔹 System Administrator / Engineer Responsible for managing servers, operating systems, and internal infrastructure. They ensure high availability, system performance, backups, and smooth day-to-day operations. 🔹 IT Security Specialist Focuses on protecting organizational data and systems. From implementing security policies to monitoring threats and ensuring compliance, they are the frontline defense against cyber attacks. 🔹 Network Engineer Designs, implements, and maintains network infrastructure (LAN/WAN). They ensure reliable connectivity, troubleshoot network issues, and optimize performance for users and systems. 🔹 App / Database Administrator Manages business applications and databases. Ensures data integrity, availability, performance tuning, and supports critical business processes. 🔹 IT Support / Helpdesk Acts as the first point of contact for technical issues. They resolve user problems, maintain productivity, and ensure minimal downtime across the organization.
0
0
🔐 Cybersecurity: Protecting the Digital Frontier
Every day, millions of attacks happen across the world —from phishing emails to ransomware and data breaches. 👉 Cybersecurity is what stands between attackers and everything we rely on: - Personal data - Businesses - Financial systems - Critical infrastructure 🧠 What Cybersecurity Really Means Cybersecurity isn’t just “hacking” or tools… It’s about: - Protecting systems from unauthorized access - Detecting threats before they cause damage - Responding quickly when something goes wrong ⚡ Why It Matters More Than Ever We live in a digital world: - Work is online - Money is digital - Communication is instant 👉 That also means risk is everywhere 🚀 Where You Fit In Whether you're a beginner or already learning: You are training to become someone who: - Spots threats others miss - Protects organizations from real attacks - Secures the future of technology 🎯 The Mission This community is here to help you: - Learn real skills - Build a strong foundation - Stay consistent - Break into cybersecurity the right way 💬 Let’s Engage 👉 What made you interested in cybersecurity?👉 What do you want to achieve in this field? Drop it below 👇🔥
0
0

Security+ Is Not the Cert the SOC Job Requires
The job posting for SOC Analyst lists Security+ as the requirement. The technical interview asks you to walk through a SIEM alert, identify the lateral movement, and explain what you would contain first. Security+ does not test that. CySA+ does — at 33% of the exam, with Wireshark, SIEM correlation, and CVSS scoring named in the objectives. Security+ covers the same territory at the vocabulary level. Both certs are CompTIA products. The boundary between them is not accidental. A candidate who earns Security+, targets a SOC role because every job posting lists it, and fails the technical screen because the interview tests CySA+ skills is now a candidate for a second cert purchase. Three separate comments on a post about this gap named CySA+ independently within 24 hours. None of them were citing the same source.
0
0

1-12 of 12
powered by

skool.com/breaking-into-cybersecurity-1366
Start your cybersecurity journey, learn core skills, prepare for certifications, and build a path into the industry. Get the roadmap you need.
Suggested communities
Powered by
